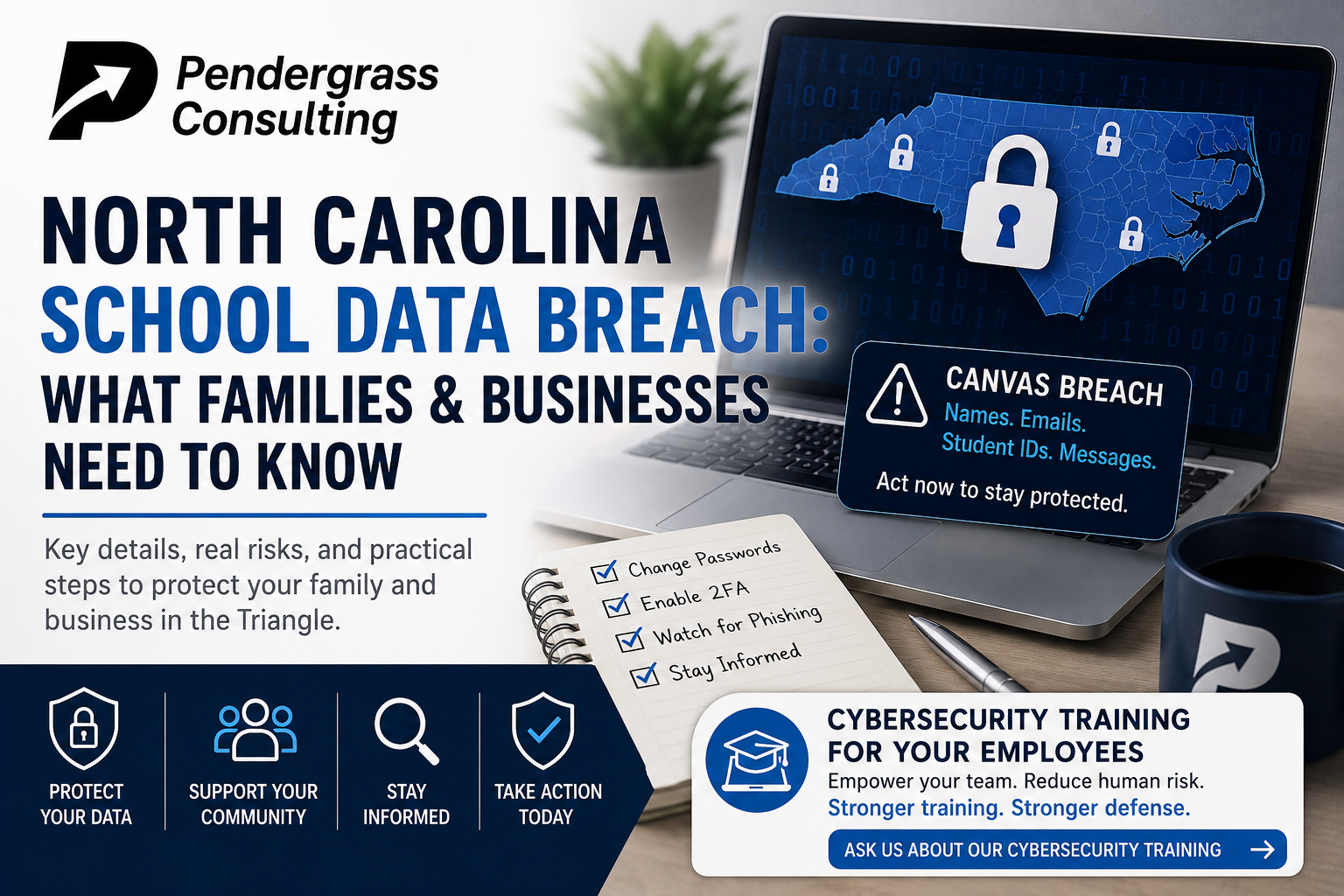
If you have a child in a North Carolina public school, your child’s data may have just been exposed in one of the largest education-sector data breaches in U.S. history. If you run a business in the Triangle, the same story has a parallel lesson that’s worth sitting with.
The Wake County Public School System issued a public notice this week confirming that personal information of staff and students may have been accessed in a cyberattack on Canvas, the statewide learning management system used across all of North Carolina’s public and charter K-12 schools, the University of North Carolina system, and the state’s community colleges. The breach affects far more than just Wake County. According to claims made by the attackers and corroborated by reporting at BleepingComputer, TechCrunch, and Inside Higher Ed, the underlying attack hit close to 9,000 educational institutions worldwide and roughly 275 million individual records.
Here’s what’s known, what it means for families and businesses across the Triangle, and what to actually do about it.
What Happened
The target was Instructure, the Salt Lake City-based company that owns Canvas. Canvas is the learning management system that teachers use to post assignments, students use to submit work, and parents use to track grades. It’s used by roughly 41 percent of educational institutions in North America, including every public school in North Carolina (NCDPI signed a statewide agreement with Instructure in 2015 to deploy Canvas across all K-12 schools).
The publicly known timeline:
- April 25, 2026 – The attackers gained access to Instructure’s cloud-hosted environment.
- April 29, 2026 – Instructure detected the intrusion and revoked the attacker’s access.
- April 30 – May 3 – Instructure disclosed the cyberattack and confirmed user data was stolen.
- May 3, 2026 – The criminal extortion group ShinyHunters claimed responsibility and listed Instructure on its dark web leak site, demanding payment under threat of releasing the data publicly. The group claims to have 3.65 terabytes of stolen data.
- May 5, 2026 – Wake County Public School System issued public notification. North Carolina Department of Public Instruction was notified.
- May 8, 2026 – The deadline ShinyHunters publicly set for institutions to pay before they release the full archive.
Instructure has confirmed that the stolen data includes names, email addresses, student ID numbers, and messages exchanged between Canvas users (students, teachers, and staff). The company says, based on the investigation so far, that passwords, dates of birth, government identifiers (Social Security numbers), and financial information were not involved. ShinyHunters disputes some of this and additionally claims that Instructure’s Salesforce instance was also compromised, which would mean additional administrative and contact data was exposed.
Who ShinyHunters Are
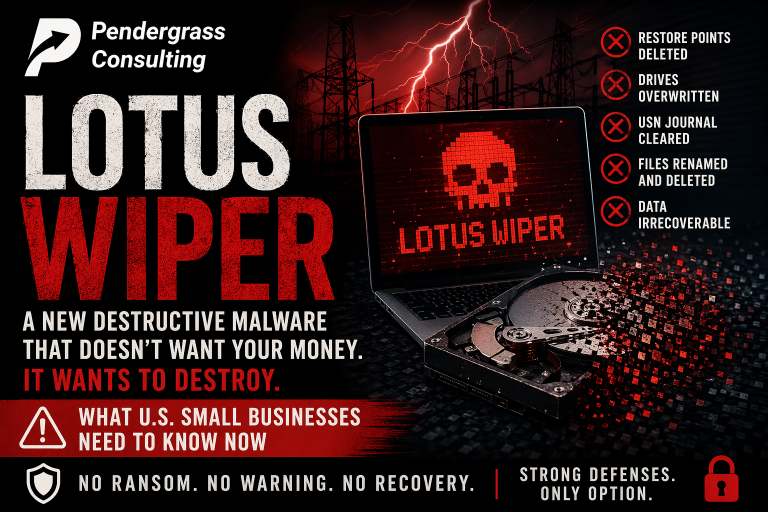
ShinyHunters is not new. They are one of the most prolific data-extortion groups operating today. Past breaches attributed to the group include attacks on Ticketmaster, Google, the University of Pennsylvania, Princeton, Harvard, the fintech lender Figure (967,200 exposed records), and Panera Bread (allegedly 14 million customer records). Their 2026 playbook is consistent: steal data, list the victim publicly on a leak site, set a deadline, demand payment, release the data if the deadline passes.
This is what’s known in the security industry as a “data extortion” operation rather than a traditional ransomware attack. The attackers don’t bother encrypting your systems. They just steal the data and threaten to publish it. For an organization like Instructure, the leverage is enormous – the public release of millions of student records is a public relations and legal nightmare regardless of whether passwords or financial data were involved.
What This Means for North Carolina Families
If your child attends a public or charter K-12 school anywhere in North Carolina, or attends UNC, NC State, a community college, or any of the dozens of other higher-education institutions in the state that use Canvas, your child’s basic identity information and possibly their school messages may be in the dataset the attackers are threatening to leak.
The good news, based on what Instructure has confirmed publicly, is that the most sensitive categories of data – passwords, Social Security numbers, dates of birth, financial information – were not part of the breach. The bad news is that names, email addresses, student ID numbers, and the content of messages between students and teachers are still extremely valuable to scammers.
Here’s why: a phishing email that says “Hi parent of [your actual child’s name], your child has a missed assignment in [actual class name they’re enrolled in] – please click here to log in and review” is dramatically more convincing than a generic phishing email. With names, schools, classes, and message history in hand, attackers can craft highly personalized phishing attacks against parents, students, and teachers. Expect a wave of these in the coming weeks and months.
What Parents and Students Should Do This Week
- Change your child’s Canvas password if they log in directly to Canvas (rather than through a school single sign-on system). Make it unique – not the same password used anywhere else.
- Change passwords on any other accounts where your child reused the Canvas password – email, gaming, social media. If they’ve ever used the same password in two places, those accounts are now potentially exposed.
- Enable two-factor authentication on every account that supports it – email, school portals, financial accounts, social media.
- Be extremely skeptical of any email, text, or call mentioning your child’s school, teacher, or coursework. The attackers now potentially have enough context to make scams feel real. If you get a message about a missed assignment, an account problem, or a fee, do not click any link in the message. Open a fresh browser tab, go to the school’s website directly, and log in from there.
- Watch for unusual activity on your child’s accounts – logins from unfamiliar devices, password reset emails you didn’t request, messages they didn’t send.
- Talk to your child about phishing. Kids and teenagers are prime targets for scams that use real personal context. The conversation doesn’t have to be technical. “If you get a message about school that asks you to log in, don’t click it – go to the school site yourself” is enough.
The Lesson for Small Business Owners in the Triangle
The Canvas breach is a textbook case of third-party vendor risk – and that’s the part of the story that small business owners need to absorb.
Wake County Public Schools didn’t get hacked. Their internal systems were not breached. They didn’t fail to patch a server. They didn’t have an employee click a phishing link. They did everything right on their end. The breach happened at a vendor they trusted with their data. And once a vendor is compromised, every single customer of that vendor is exposed – regardless of how good their own security is.
This is the same pattern that’s hit small businesses repeatedly over the past two years. PowerSchool was breached in late 2024. Snowflake customers were attacked in 2024. The MOVEit file transfer vulnerability in 2023 cascaded across thousands of organizations. In each case, the underlying business that got robbed had effectively zero ability to prevent it. Their data was lost because they had handed it to someone else.
For a small business in Raleigh, Cary, Selma, or anywhere else in the Triangle, the question this raises is uncomfortable but important: whose hands is your data in right now, and what happens if any of those vendors gets breached?
- Your accounting software vendor
- Your CRM provider
- Your payroll processor
- Your email and document collaboration platform
- Your industry-specific practice management software (legal, medical, real estate, etc.)
- Your e-commerce platform
- Your cloud hosting provider
- Every SaaS tool your team has subscribed to in the last five years
Each one is a Canvas-shaped risk. Each one holds a piece of your business’s data. Each one can get breached – regardless of what you do internally. The defense isn’t “trust them less.” It’s understanding what data they hold, what would happen if they lost it, and having a plan for the customer-notification, password-reset, and reputational fallout that follows.
What Small Businesses Should Take Away
- Inventory your vendors. Make a list of every cloud service, SaaS platform, and external IT provider that holds any data about your business, your employees, or your customers. Most small businesses have never made this list, and are surprised by how long it is.
- Know what each vendor holds. For each one, know what data is stored there. Customer records? Employee SSNs? Financial information? Intellectual property?
- Use unique passwords on every vendor account. If your accounting software gets breached and you reused that password on your bank, your bank is now exposed too. Use a password manager.
- Enable multi-factor authentication everywhere. Especially on anything that holds customer or financial data.
- Have a notification plan. If a vendor of yours announces a breach next month, do you have an established process for figuring out what your exposure is, communicating with affected customers, and offering them remediation? Most small businesses don’t, and they end up scrambling.
- Train your team to expect personalized phishing. Breaches like this one give attackers the raw material to make their scams more convincing. Your team needs to understand that “this email mentions real details about my work” doesn’t make it real.
How Pendergrass Consulting Helps
Vendor risk, breach response, and employee training are exactly the areas where small businesses most often have gaps – because nobody whose job it is to think about these things is on staff. That’s where we come in.
Our managed cybersecurity service for small businesses across the Triangle includes:
- Vendor inventory and risk assessment – so you know what data is sitting where, and what your exposure looks like if any one vendor gets breached
- Account security hardening across the SaaS platforms your business depends on – multi-factor authentication, password policy, admin access reviews
- Security awareness training for employees built around real, current threats – including the post-breach phishing campaigns that always follow stories like this one
- Incident response planning so you have a real playbook for what to do if a vendor of yours announces a breach affecting your customer data
- Quarterly reviews where we walk through what we changed, what we found, and what’s coming next
If you’ve never had a real conversation about which vendors hold your business’s data, what you’d do if any of them got breached, or whether your team would recognize a personalized phishing attack that referenced real details about your business – that’s what we mean by a comprehensive small business environment review. There’s no charge and no commitment for the first conversation.
Pendergrass Consulting
Phone: 252-432-3325
Email: Sales@PendergrassConsulting.com
110 S. Massey St., Suite 201, Selma, NC 27576
Pendergrass Consulting is a full-service IT firm based in Selma, NC, serving small businesses and families across the Research Triangle, Raleigh, Cary, Wake County, Johnston County, and nationally for web, hosting, email, cloud backup, cybersecurity, and digital marketing services.